Terraform Collaboration Challenges and How to Tackle Them
By Idego Group
For those unfamiliar with Terraform, the article recommends reading an introduction to Infrastructure as Code first to understand Terraform's basic workflow.
Problem: Shared Access to State File and Encryption
Terraform stores state files locally by default, which works for individual engineers but creates challenges in collaborative environments. Multiple engineers need access to consistent data, requiring a shared storage location. Simultaneous access to the same file can cause conflicts, data loss, or corruption, necessitating file locking mechanisms.
Version control systems like GitHub seem ideal but present a critical issue: all data in the state file is stored in plain text. This prevents storing sensitive information in version control. Additionally, human error poses risks - developers may forget to pull the latest version before running Terraform, potentially rolling back infrastructure accidentally.
Solution: Remote Backend
Terraform's remote backend solves these issues by storing state files in shared locations. When using Microsoft Azure, Storage Account is recommended because it provides file locking and encryption together with additional, optional features like file versioning.
Problem: Terraform Version Incompatibility
Different engineers using different Terraform binary versions can cause issues, as state file organization changes between major releases. State files aren't universally compatible across versions, and Terraform code may not remain backward compatible.
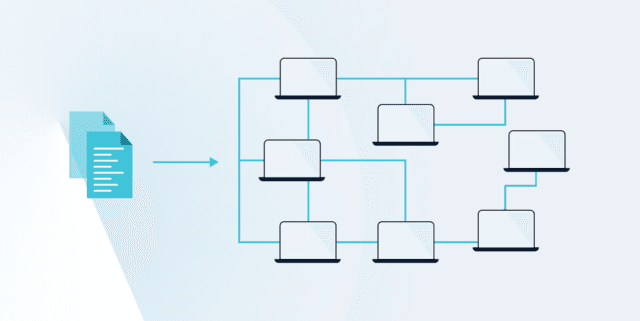
Solution: CI/CD Integration
Integrating Terraform with CI/CD pipelines in Jenkins or Azure DevOps ensures consistent tooling and version management.
Problem: Code Review and Plan Visibility
Teams need infrastructure change visibility and peer review before deployment occurs.
Solution: Atlantis Tool
Atlantis automates Terraform Pull Request workflows, enabling teams to run terraform plan and apply commands directly from pull requests. The tool comments with output on PRs, allowing review before approval and deployment. The key advantages include error prevention through code review, ensuring approved code reaches protected branches, and eliminating concerns about Terraform binary versions and credentials.